Error during jitsi-meet-tokens installation - Install & Config - Jitsi Community Forum - developers & users

Secure cryptographic functions via virtualization‐based outsourced computing - Qiang - 2016 - Concurrency and Computation: Practice and Experience - Wiley Online Library
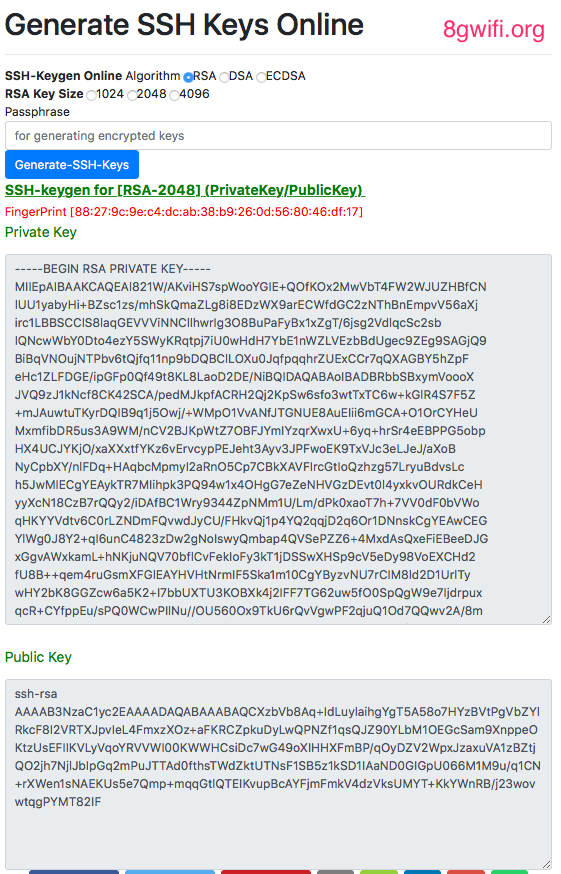
How does RSA get a pem string, and then how does RSA convert a pem string to RSA · Issue #10770 · openssl/openssl · GitHub