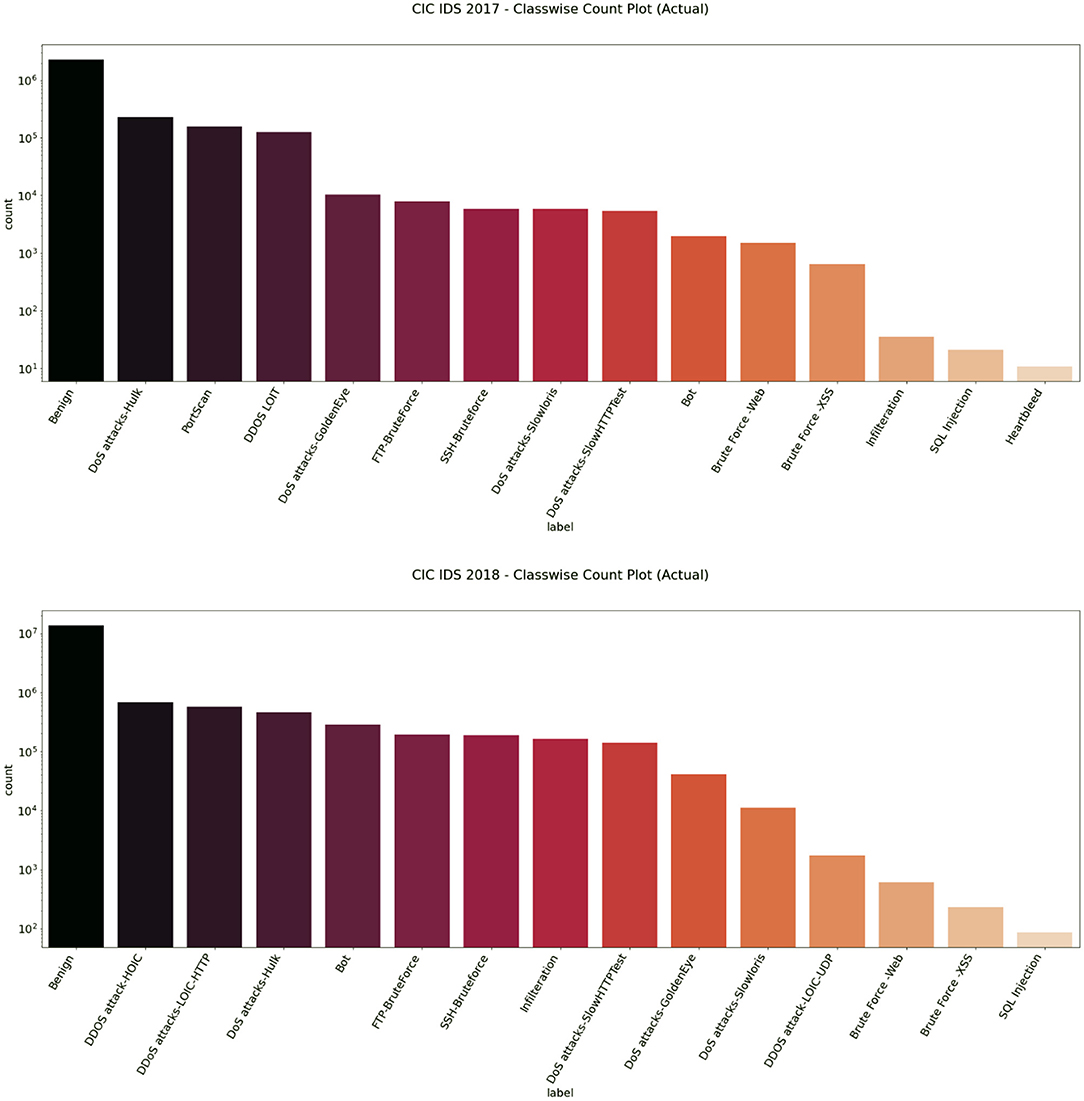
Electronics | Free Full-Text | Toward Developing Efficient Conv-AE-Based Intrusion Detection System Using Heterogeneous Dataset | HTML

LiXiongBao Glowing Alarm Clock 7 LED Color, Digital Alarm Thermometer Night Glowing Cube 7 Colors Clock LED Change LCD with Data and Temperature Display for Bedroom Child (Changeable Color) : Amazon.ca: Home
![Cisco IOS XR System Monitoring Configuration Guide for the Cisco CRS Router, Release 6.1.x - Implementing and Monitoring Alarms and Alarm Log Correlation [Cisco IOS XR Software (End-of-Sale)] - Cisco Cisco IOS XR System Monitoring Configuration Guide for the Cisco CRS Router, Release 6.1.x - Implementing and Monitoring Alarms and Alarm Log Correlation [Cisco IOS XR Software (End-of-Sale)] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/100001-200000/110001-120000/117001-118000/117361.eps/_jcr_content/renditions/117361.jpg)
Cisco IOS XR System Monitoring Configuration Guide for the Cisco CRS Router, Release 6.1.x - Implementing and Monitoring Alarms and Alarm Log Correlation [Cisco IOS XR Software (End-of-Sale)] - Cisco
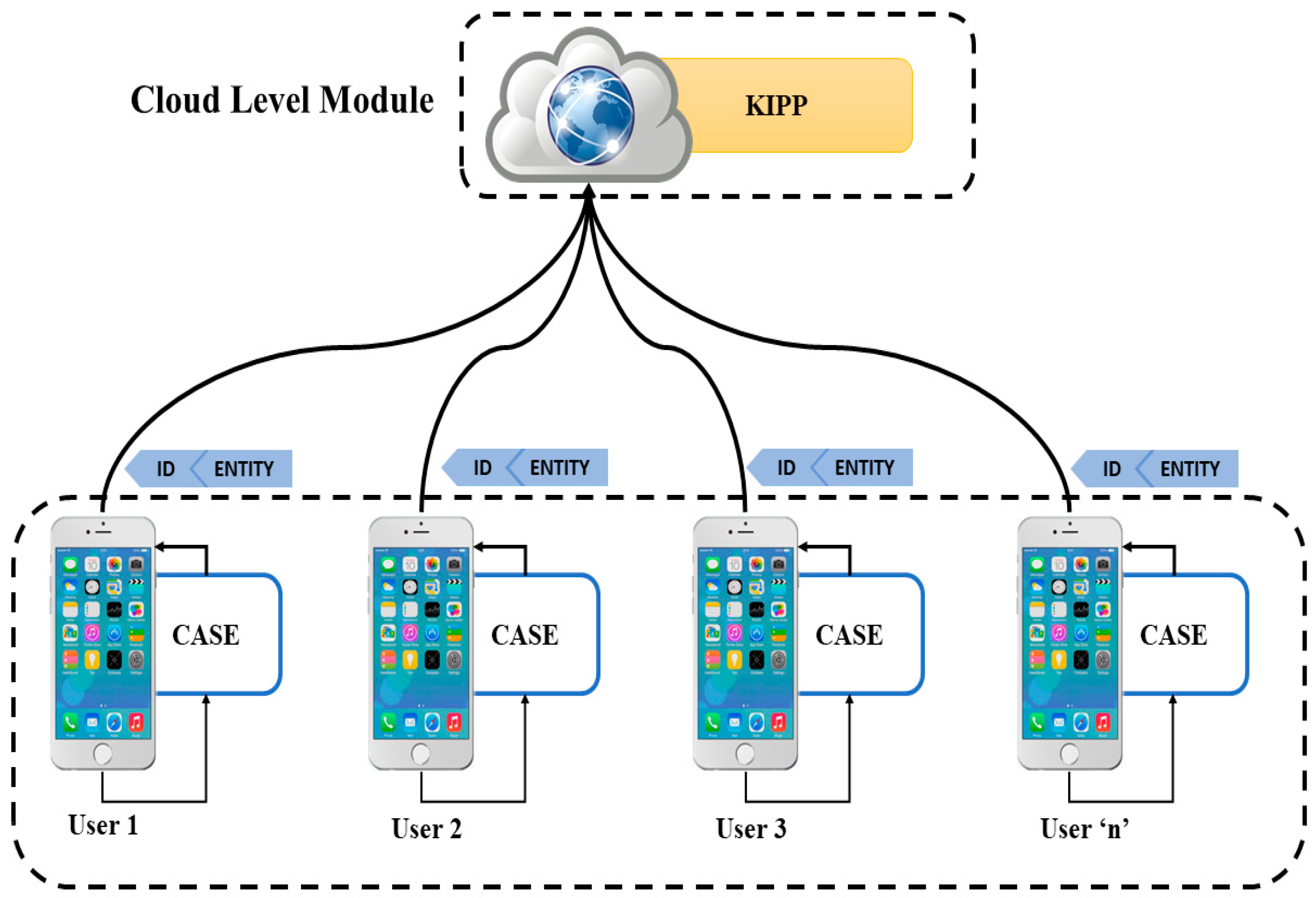
Applied Sciences | Free Full-Text | MaLang: A Decentralized Deep Learning Approach for Detecting Abusive Textual Content | HTML

Anomaly‐based intrusion detection systems: The requirements, methods, measurements, and datasets - Hajj - 2021 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library

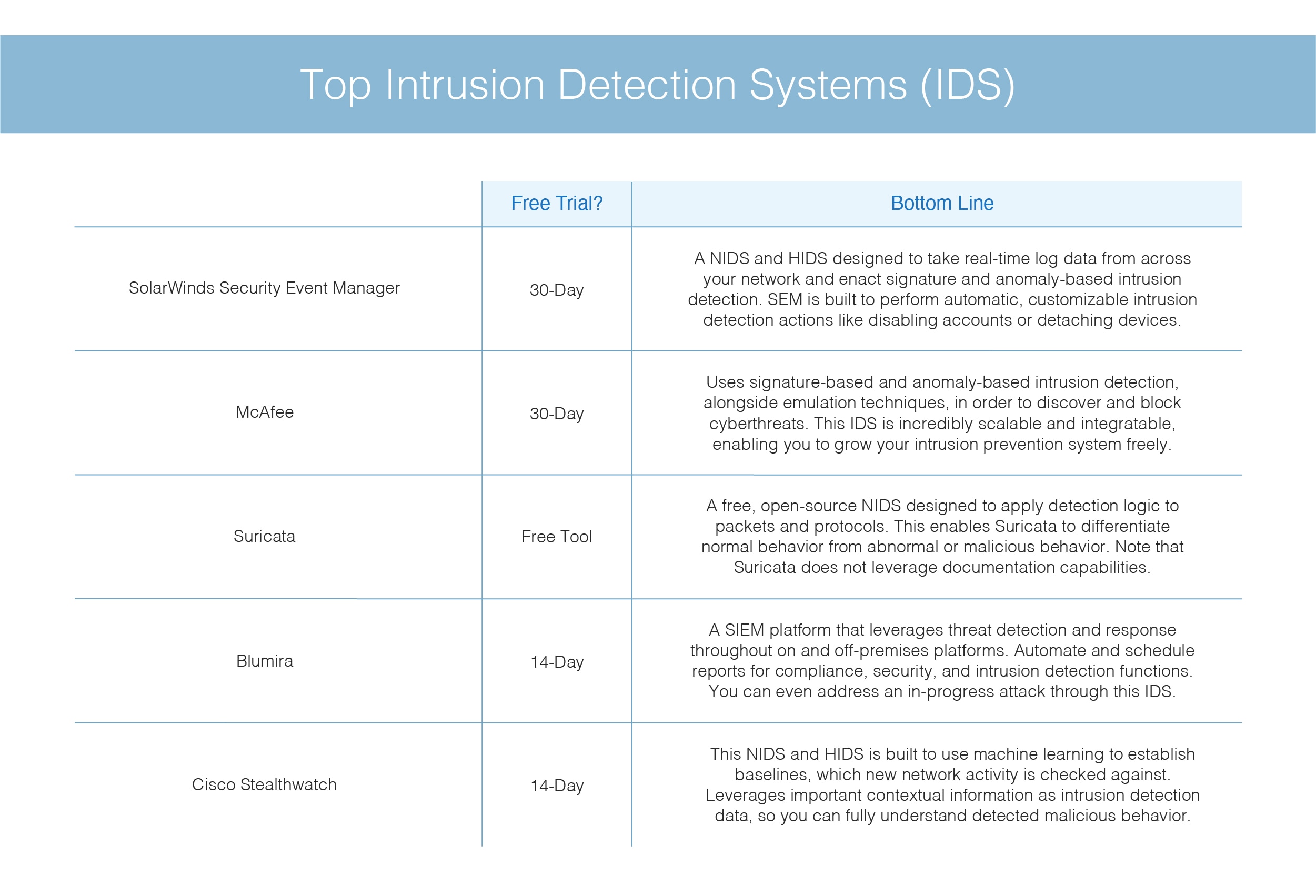
What Is Intrusion Detection and Prevention System? Definition, Examples, Techniques, and Best Practices | Spiceworks It Security

What Is Intrusion Detection and Prevention System? Definition, Examples, Techniques, and Best Practices | Spiceworks It Security