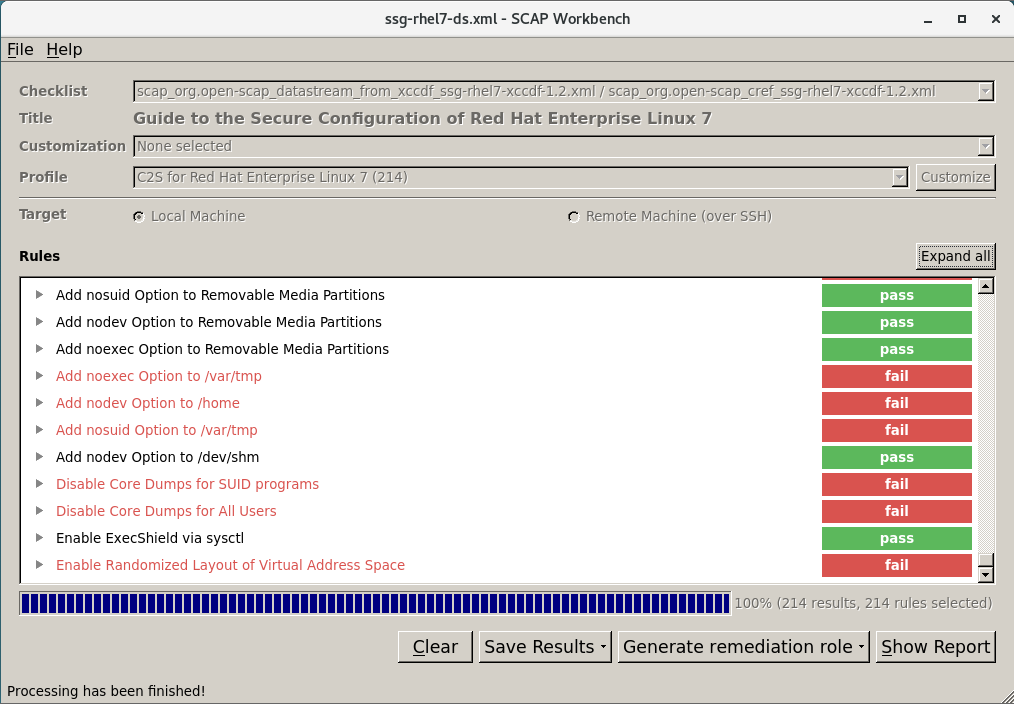
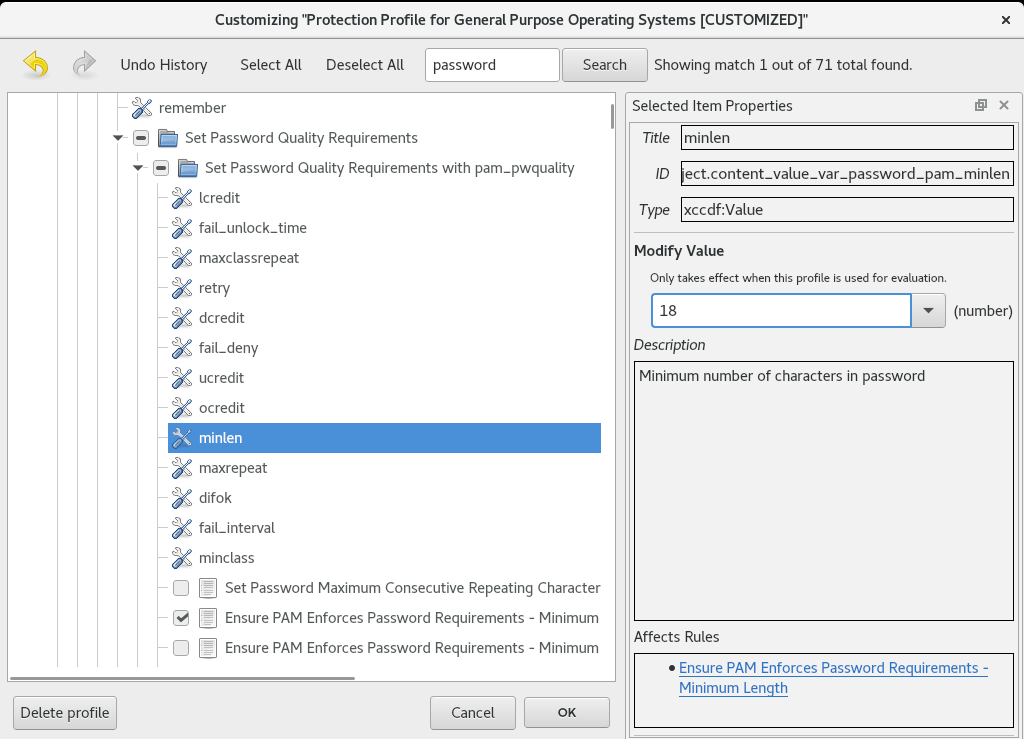
8.7. Scanning the System with a Customized Profile Using SCAP Workbench Red Hat Enterprise Linux 7 | Red Hat Customer Portal

8.7. Scanning the System with a Customized Profile Using SCAP Workbench Red Hat Enterprise Linux 7 | Red Hat Customer Portal
:format(webp):quality(100)/http://static2.playtech.ro/wp-content/uploads/2016/11/chkdsk.jpg)










:format(webp):quality(100)/http://static2.playtech.ro/wp-content/uploads/2016/11/Windows-10-chkdsk-scan-now.jpg)